Cyber security is a growing concern among merchants, web site owners, health care providers, banks, and pretty much anyone with an online presence – and that includes you. This week I’m going to provide a demonstration of how “phishing” works. Phishing, much like one of our favorite Kentucky pass times, “fishing”, is all about the bait and hook.
Usually this starts with a compelling email about one of your accounts. It can be a bank account, UPS, Facebook, or any other account that requires a username and password, credit card number, or any other sensitive data. There is usually a plea of urgency like, “if you don’t respond within the next 24 hours we will be forced to cancel your account.” That should be one of your first clue’s.
Secondly, the email sometimes be worded in a way that makes it obvious that the writer’s primary language is not English. The misuse of pro-nouns, or uncommon verbs are often good indicators. For instance, instead of “Please contact us within the next 24 hours” it might read, “Please communicate with us within the next 24 hours.” That was kind of subtle, but we typically would not use the word communicate in English when requesting action from an individual. “It would be well if we hear from you soon” instead of “It would be good if we hear from you soon” is another “well” example 🙂
Thirdly, the call to action will usually ask you to visit a web site and they provide you with a link. The more developed “Phishers” will hide the actual link so that it does not show up in the email. However, most email readers, including Outlook will show you the actual link if you hover over it with your mouse. Always do this prior to clicking on it to confirm the link is owned by the party that is supposedly contacting you. Sometimes even this can be tricky – let me show you an example….
Here is a phishing email I actually received this week….
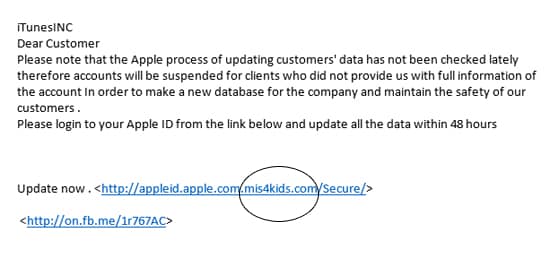
Notice that the link they provide (and they didn’t hide it) looks like an Apple owned address. But always check the URL/domain right before the last TLD (.com, .net, .org, etc.). This address initially appears to be an apple.com address, but if we go all the way to the end, we can clearly see it is an mis4kids.com address. DON’T CLICK ON IT. I didn’t check this one, but I assume that the resulting web site will either immediately download malware to my computer, or will ask me to enter my Apple ID information so they can create havoc in that way.
So in this one email we can see all three examples…
A) Urgent Call to Action – I must respond within 48 hours.
B) Poor use of English Language – this is a really long run on sentence that is very vague.
C) Fake URL – a URL is provided that is intended to look like a reputable company’s domain.
So watch out for these key signs that someone is Phishing for your information and don’t bite the hook.

