It was predicted that in 2019, global cybercrime-related costs would surpass $2 trillion. Yet 68% of all US businesses still haven’t purchased any type of data breach or cyber liability coverage. The most common types of cyber attacks are phishing, network intrusion, and stolen and/or lost devices or records. And while industries such as transportation, healthcare, and manufacturing are at a higher risk than others, that doesn’t mean any business is safe. Especially since by 2021, another business is predicted to fall to a ransomware attack every 11 seconds. The statistics are staggering, but that doesn’t mean a company can’t protect themselves from the various types of cyber attacks. But first, they need to know what types of network attacks to look out for.
We want to help your business stay safe. Keep reading to learn about the five most common cyber attacks.
Phishing happens when someone receives a fraudulent email that appears as though it’s coming from a trusted source, like your bank. The goal is to gain your trust so you provide the hacker with your personal information or you take the action they want you to in order to gain that information.
Here’s how to protect you and your company from phishing:
Never open anything from anyone whose email address you don’t recognize until you’ve deemed that they’re from a credible source.
These attacks happen when a hacker puts themselves in between two-party transactions. Once they interrupt the traffic, attackers can filter and steal data. A popular way for a hacker to steal data is when you use unsecured public Wi-Fi to conduct your business. Once you’ve been breached, the attacker can install software to access all your information. Always make sure you only use secured Wi-Fi, especially if you’re traveling.
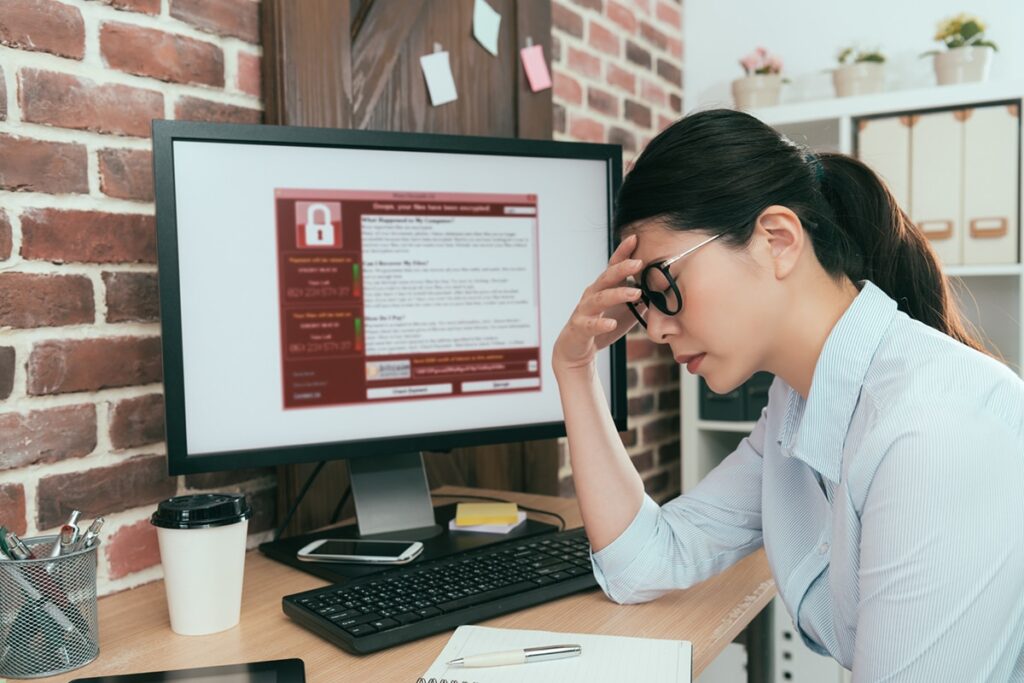
A malware attack stems from unwanted software that’s installed in your system without your knowledge or consent. Once in your system, it can attach itself to legitimate code and propagate, replicate itself, or hide in useful applications.
The most common types of malware are:
Stealth viruses conceal infected areas and can change the records of files.
DoS attacks can flood your networks, systems, and/or servers with traffic that exhaust your bandwidth and your resources. It prevents legitimate requests from being carried out. While there are no benefits to this type of attack, the aim is usually to force you to take your system offline so hackers can launch a different type of attack.
Sadly, the most common passwords are still “Password” and “123456.” And because passwords are used to authenticate users to private information, it’s imperative you keep your password safe. Hackers use brute-force attacks, which means they try different, passwords hoping one will work. Usually, hackers use your name, job title, or hobby to guess. A dictionary attack happens when hackers copy an encrypted file that contains passwords. They then apply the same encryption to a dictionary of other commonly used passwords. Hackers then compare the results.
Unfortunately, there are more types of cyber attacks out there. And often, companies are completely unaware of how easy it is to implement policies and strategies to keep their information safe.
We can help you keep your company information safe from prying eyes. Contact us to get a free quote.
Just fill out and submit the form below and someone will contact you as soon as possible.
The UPS Store
1619 Bypass Rd. Suite 122
Winchester, KY 40391
Virtual Office Space
710 E Main St Suite 110
Lexington, KY 40502